GitHub is the most important platform for version control and collaboration among developers worldwide, housing millions of repositories and a vast user base.
Despite its reputation as a trusted platform, ensuring security on GitHub requires proactive measures by its users.
With the potential for malicious code and unauthorized access, developers must be vigilant in securing their repositories.
To help you prevent practically all the issues that might occur, we will talk about essential ways to enhance your GitHub security.
Best Practices for Staying Safe on GitHub
While GitHub can be used securely, there are best practices to follow to ensure you avoid unnecessary risks:
1. Use a Virus Scanner
Downloading code from GitHub can be risky, especially when pulling from unfamiliar repositories.
Virus scanners add a crucial layer of security by identifying potential malware before it has a chance to compromise your system.
This precaution becomes essential when dealing with open-source projects or code from lesser-known developers.
- Scan all downloaded code: Always run code through a virus scanner to detect hidden threats. That should be standard practice for any downloaded file, particularly those you plan to compile or run.
- Use reputable security software: Quality antivirus programs, like those offered by trusted brands such as NordVPN, McAfee, or Norton, offer advanced detection tools for malware and other security risks.
- Consider automated scanning: Some security suites can automatically scan files downloaded to specific folders, saving time and ensuring that all incoming files are checked before you even interact with them.
2. Protect Your Login Credentials
Securing your GitHub account starts with robust login practices, as weak or compromised credentials often open doors to unauthorized access.
By combining a strong password with two-factor authentication (2FA), you create a solid defense against hacking attempts.
GitHub’s 2FA adds an extra verification step, making it significantly harder for intruders to access your account, even if they somehow obtain your password.
- Use a Strong Password
- Choose a unique password that combines uppercase and lowercase letters, numbers, and special characters.
- Avoid using common passwords or those tied to personal information (e.g., birthdays, names).
- Regularly update your password to minimize potential risks.
- Enable Two-Factor Authentication (2FA)
- Go to GitHub’s settings to enable 2FA, which requires a secondary code when logging in.
- Opt for an authenticator app (like Google Authenticator) over SMS, as it offers better security.
- Save backup codes in a secure location to ensure account access if you lose your primary 2FA device.
- Avoid Password Reuse
- Use a unique password for GitHub that’s not shared across other platforms or accounts.
- Consider using a password manager to securely store and generate unique passwords.
- Monitor for Suspicious Login Activity
- Regularly review your GitHub account’s security log for any unfamiliar login attempts or actions.
- If you suspect unauthorized access, update your credentials and enable any additional security measures.
3. Adjust Repository Settings
To protect your code and data, it’s essential to optimize your GitHub repository settings.
| Action | Description |
|---|---|
| Set Repositories to Private | For sensitive projects, switch to private mode. It restricts access to invited users only, preventing unauthorized duplication or misuse. |
| Limit Access to Essential Contributors | Grant access only to team members actively involved in the project, reducing the chance of accidental leaks or unauthorized changes. |
| Regularly Review Access Permissions | Periodically review repository access, especially when contributors join or leave, to prevent unnecessary access. |
| Revoke Access for Departing Team Members | Immediately revoke access for team members or contractors who leave to avoid potential security issues. |
| Double-Check Settings for Sensitive Projects | For high-value projects, double-check settings to ensure that collaborator roles and access levels align with current project needs. |
4. Keep Sensitive Data Secure
Protecting sensitive data within repositories is critical for maintaining security, preventing unauthorized access, and avoiding potentially costly misuse.
| Action | Description |
|---|---|
| Avoid Storing Sensitive Data in Repositories | Refrain from including sensitive data, such as API keys, passwords, or credentials, in repositories, especially public ones. |
| Abstract Sensitive Data to Secure Storage | Use environment variables or secure config files to store sensitive data instead of hard-coding it. |
| Implement Backend-Only Access for Credentials | Store sensitive data in the backend, restricting access to authorized systems or developers and reducing exposure to unauthorized users. |
| Use GitHub Secrets for Sensitive Information in CI/CD | For CI/CD workflows, store sensitive information in GitHub Secrets to encrypt and limit access to environment variables securely. |
5. Evaluate Repository Popularity and Activity
When choosing repositories on GitHub, evaluating their popularity and activity level provides insight into the project’s reliability and safety.
Projects with a strong reputation and consistent maintenance are less likely to contain malicious or outdated code.
Here’s what to look for:
Check the Contributor Count
Repositories with multiple contributors are generally more reliable.
A larger contributor base often means a more collaborative and vetted project, reducing the likelihood of malicious code slipping through unnoticed.
Tip: Look for active contributors who regularly add value, address issues, and participate in discussions.
Review the Star Count
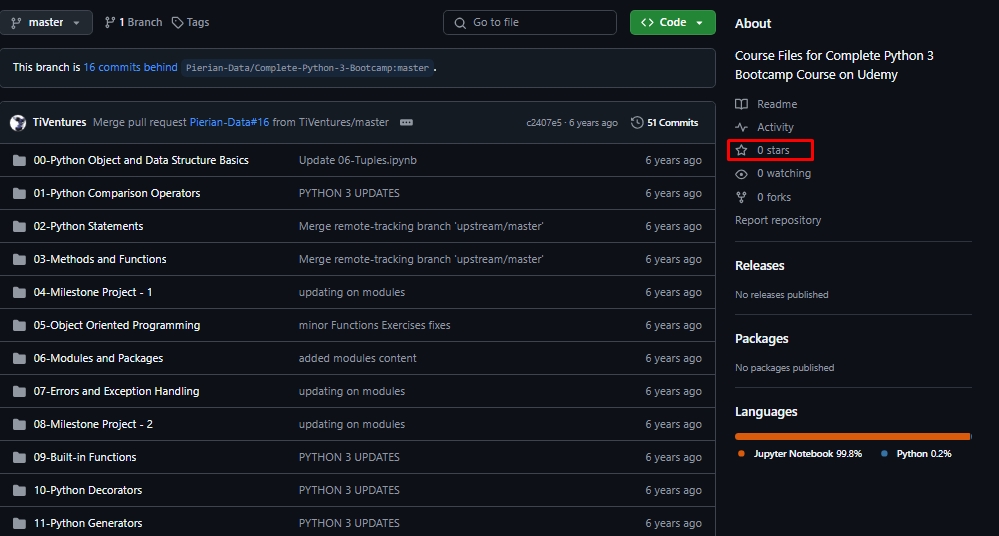
Stars on a repository serve as a measure of community trust and interest. High-starred projects are often considered safer and more trustworthy, as many users rely on them.
While not foolproof, a high star count usually indicates positive community feedback.
Analyze Commit Frequency
Regular commits demonstrate that the repository is actively maintained.
A consistent update history means that issues are likely to be addressed promptly and that the project is less likely to be abandoned.
Tip: Avoid repositories with sporadic or outdated commits, as they may lack recent security patches.
Look for a Record of Bug Fixes
Projects with a clear history of addressing bugs and vulnerabilities signal a commitment to quality and security.
Check the issue tracker and pull request history for resolved bugs and security fixes, as this demonstrates that the maintainers prioritize stability.
Evaluate Community Engagement
Repositories with strong community engagement tend to be safer.
Community interaction, such as responsive maintainers, discussions, and feedback, provides an extra layer of security as issues are identified and resolved collaboratively.
6. Inspect the Repository
For critical projects, a manual inspection of the repository is an essential step to ensure security.
It is an approach that allows you to catch potential issues that automated tools might miss and adds a layer of defense.
While it can be time-consuming, this inspection is valuable in protecting your codebase.
| Step | Description |
|---|---|
| Examine the Code Structure | Look for unusual files or directories that don’t match the expected structure. Malicious code may be hidden in disguised or unconventional files. |
| Check for Obfuscated Code | Be cautious of hard-to-read or obfuscated code, often used to conceal harmful instructions. Watch for excessive abbreviations or lack of documentation. |
| Review External Dependencies | Examine third-party libraries included in the project, verify their sources, and check for outdated versions or known vulnerabilities. |
| Search for Suspicious Scripts | Look for unexpected scripts, especially those running on startup. Non-essential scripts may indicate malicious intent. |
| Evaluate Code Quality and Comments | High-quality code is organized and documented. A lack of comments or inconsistent formatting may indicate hidden risks. |
| Test in a Secure Environment | Run the code in a sandbox or virtual machine to safely observe its behavior, especially for unverified sources. |
Is It Safe to Download from GitHub?
| Step | Description |
|---|---|
| Check Repository Owner | Look for verified profiles and active history to ensure credibility. |
| Read the README File | Review the README for project details and installation steps. |
| Watch for Security Warnings | Avoid repositories with unresolved security alerts. |
| Examine Third-Party Code | Check that third-party dependencies are from trusted sources. |
GitHub’s Security Limitations
GitHub provides a robust platform for developers to manage, store, and share code collaboratively. However, its design prioritizes ease of collaboration over built-in security measures, making user vigilance essential.
To maintain security on GitHub, developers should be aware of its limitations and take additional precautions.
| Limitation | Description |
|---|---|
| User-Managed Security | It relies on users to manage their security settings. Actions like setting strong passwords and enabling two-factor authentication are essential for protecting repository access. |
| Private Repositories Provide Limited Protection | Setting a repository to private hides it from public view, but it doesn’t prevent all security threats. Strong account security is still necessary, and collaborators can access and clone the code. |
| No Built-in Virus Scanning | It doesn’t scan uploaded files for viruses or malware, so users should manually scan downloaded code and only use trusted sources. |
| Open Collaboration and Potential Exposure | GitHub’s open nature enables easy forking and cloning but can expose code to risks if security practices aren’t followed. Access should be carefully managed, especially for sensitive projects. |
| Responsibility for Sensitive Data Protection | GitHub doesn’t protect sensitive data like API keys or credentials. Developers must keep sensitive data out of the codebase or securely stored in the backend to prevent exposure. |
Potential Risks When Using GitHub
| Risk | Description |
|---|---|
| Downloading Repositories | Code from unfamiliar or unverified repositories can contain malicious elements like keyloggers. Run downloaded code through a virus scanner before compiling or executing it. |
| Hacking Repositories | Poor security practices, such as weak passwords or lack of 2FA, make repositories vulnerable. Use strong passwords and enable two-factor authentication to prevent unauthorized access. |
| Viruses in Code | GitHub hosts some malware repositories for educational purposes, but malicious files can also be uploaded under the guise of normal projects. Caution is essential when downloading code. |
Final Thoughts
GitHub is a powerful tool that’s as safe as the measures developers take to protect themselves.
While GitHub itself doesn’t enforce security, implementing strong passwords, scanning code for malware, and following Git best practices can prevent most security issues.
The platform’s collaboration potential and role in version control make it essential for developers, but caution is key to avoid becoming a target for hackers.
Follow these safety tips to make the most of GitHub without compromising your data or code security.

